Analyzing malicious activities and detecting adversarial behavior in cryptocurrency based permissionless blockchains: An Ethereum usecase
Abstract
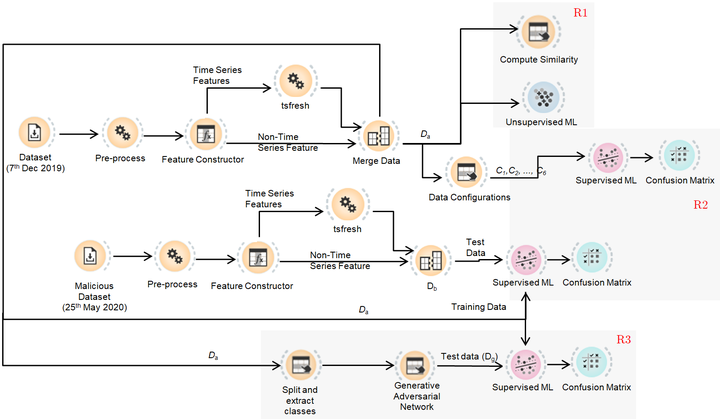
Different malicious activities occur in cryptocurrency-based permissionless blockchains such as Ethereum and Bitcoin. Some activities are due to the exploitation of vulnerabilities which are present in the blockchain infrastructure, some activities target its users through social engineering techniques, while some activities use it to facilitate different malicious activities. Since cryptocurrency-based permissionless blockchains provide pseudonymity to its users, bad actors prefer to carry out transactions related to malicious activities on them. Towards this, we aim at automatically flagging blockchain accounts as suspects that indulge in malicious activities, thus reducing the unintended support that cryptocurrency-based permissionless blockchains provide to malicious actors. We first use the cosine similarity metrics to study the similarities between the feature vector of accounts associated with different malicious activities and find that most of the malicious activities associated with the Ethereum blockchain behave similarly. We then use the K-Means clustering algorithm to check if accounts associated with similar malicious activities cluster together. We also study the effect of bias on the performance of a machine learning algorithm, due to the number of accounts associated with a malicious activity. We then compare the different state-of-the-art models and identify that Neural Networks (NN) is resistant to bias associated with a malicious activity and is also robust against adversarial attacks. The previously used ML algorithms for identifying malicious accounts also show bias towards an over-represented malicious activity.